Hydra магазин наркотиков
62K 1 мин. Мещанский районный суд Москвы 11 апреля заключил под стражу некоего Дмитрия Павлова. Его арестовали по делу о производстве, сбыте и распространении наркотиков (ч. 5 ст. 228.1 УК РФ), следует из карточки на сайте суда. Агентство «Москва» уточняет, что у арестованного мужчины отчество Олегович. Его полного тезку власти США называют одним из основателей онлайн-площадки по продаже наркотиков omg.Минюст США 5 апреля объявил об уголовных обвинениях против 30-летнего Дмитрия Олеговича Павлова, жителя России, в связи с делом omg. Его обвинили в сговоре с целью распространения наркотиков и отмывании денег. В тот же день полиция Германии сообщила, что «обезвредила серверную инфраструктуру» omg. Были конфискованы биткойны на сумму, эквивалентную примерно €23 кракен млн. Сам Павлов 6 апреля сказал BBC, что американские власти на него не выходили, и про обвинения он узнал от журналиста.omg запустили в 2015 году. Он считается крупнейшим российским даркнет-рынком, который начинал с торговли наркотиками. На середину 2019 года на ресурсе было зарегистрировано 2,5 млн аккаунтов. В основном транзакции на omg осуществлялись в криптовалюте. Эксперты считают, что omg устойчива «из-за сотрудничества со спецслужбами».Подробнее читайте в публикации «Ъ» «"ОМГ" отрастила головы».
Hydra магазин наркотиков - Кракен 2022
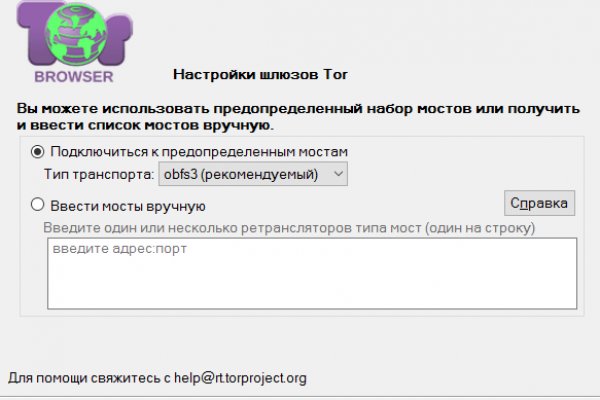
Магазины с небольшим оборотом, которые могут себе позволить небольшой простой бизнес, зная о позиции крупных игроков, копируют эту модель поведения рассказал «Ленте. Работу прекратил рынок Monopoly Market, торгующий наркотиками. Он добавил, что руководители магазинов «Гидры» начинают поиск альтернативных способов продажи запрещенных веществ. Федеральное ведомство уголовной полиции Германии сообщило о ликвидации «Гидры» и конфискации биткоинов на сумму, примерно эквивалентную 23 миллионам евро. Работа всех магазинов на «Гидре крупнейшем в мире нелегальном онлайн-маркетплейсе по продаже наркотиков, поставлена на паузу после того, как немецкие силовики отключили его серверы. По данным Минюста США одним из владельцев сайта является 30-летний российский бизнесмен Дмитрий Павлов, при этом сам он отрицает какое-либо участие в деятельности «Гидры». «Недаром у "Гидры" три головы одну отрубят, есть еще две, так и первая отрастает обратно эта плоская шутка была популярна на самой площадке и связанных с ней форумах долгие семь лет, но теперь над ней никто не смеется. Неопределенности сложившейся вокруг «Гидры» ситуации добавляет и то, что владельцы магазинов и курьеры работали анонимно. В то же время многие площадки занимают промежуточную позицию: реанимируют работу, но не уходят к конкурентам «Гидры опасаясь мести. Из 11 доменов активны оказались только два, оба ведут на сайт-визитку Русинмедиа. Для того чтобы войти на рынок ОМГ ОМГ есть несколько способов. Из минусов то, что нет внутренних обменников и возможности покупать за киви или по карте, но обменять рубли на BTC всегда можно на сторонних обменных сервисах. Многие из них не так эффективны, как хотелось. Этот сайт упоминается в социальной сети Facebook 0 раз. Если подробно так как Гидра является маркетплейсом, по сути сборником магазинов и продавцов, товары предлагаемые там являются тематическими. Окончательно портит общее впечатление команда сайта, которая пишет объявления всеми цветами радуги, что Вы кстати можете прекрасно заметить по скриншоту шапки сайта в начале материала. Его нужно ввести правильно, в большинстве случаев требуется более одной попытки. Относительно стабилен. Форум Меге это же отличное место находить общие знакомства в совместных интересах, заводить, может быть, какие-то деловые связи. Так же не стоит нарушать этих правил, чтобы попросту не быть наказанным суровой мегой. Таким образом, интернет пользователи абсолютно с любых точек земного шара получают доступ к желаемым сайтам или интернет - магазинам. Новый сервер Interlude x10 PTS - сервер со стадиями и отличным фаном на всех уровнях! Ссылки на главной странице Отношение исходящих ссылок к внутренним ссылкам влияет на распределение веса страниц внутри сайта в целом. PGP, или при помощи мессенджера Jabber.
Style & Lifestyle100% made in Europe 🇪🇺Créateurs &
artisanatEspace ClientSearch for: Suivez-nous !
² Navigation\\ Le E-shop //Déco& MaisonAccess/vêtementKidsThés &bien-êtrePapèterieBijouxActus/blogLa petitehistoirePresseInfospratiquesPanierAccess/vêtement
Kids
Déco & Maison
Papèterie
Bijoux
Thés & bien-être
CGV / Paiement / Livraison / Infos pratiquesSuivez-noussur Facebook /Pinterest / InstagramNous utilisonsdes cookies pour vous garantir la meilleure expérience sur notresite. Si vous continuez à utiliser ce dernier, nous considéreronsque vous acceptez l'utilisation des cookies.J'accepteEn savoir plus
